File sharing is one of those things that feels harmless until it is not. A link gets copied into the wrong chat. A supplier still has access three months after the project ends. A folder meant for one client is visible to five. Nothing looks dramatic at the time, yet those small shortcuts add up quickly.
That is why secure file sharing matters so much in 2026. It is no longer just about where files live. It is about who can open them, who can forward them, how long they stay available, and how easily you can prove what happened if something goes wrong.
The trick is not to make sharing painful. The trick is to make it controlled enough that people can still get their work done without spraying access all over the place.
Why file sharing becomes messy so quickly
Most businesses do not set out to create permission chaos. It grows from perfectly sensible decisions made at speed.
A team launches a new client project and opens a shared folder. A freelancer needs access “for the week”. Someone sends a link from a personal cloud account because the company system feels clunky. Another colleague adds a guest account because a supplier cannot wait until Monday. Six months later, nobody remembers who still has access, which links are public, or which files are being duplicated across tools.
This is one reason permission sprawl keeps creeping back. Modern collaboration tools are convenient by design. They are built to remove friction, and that usually means making sharing easier than reviewing.
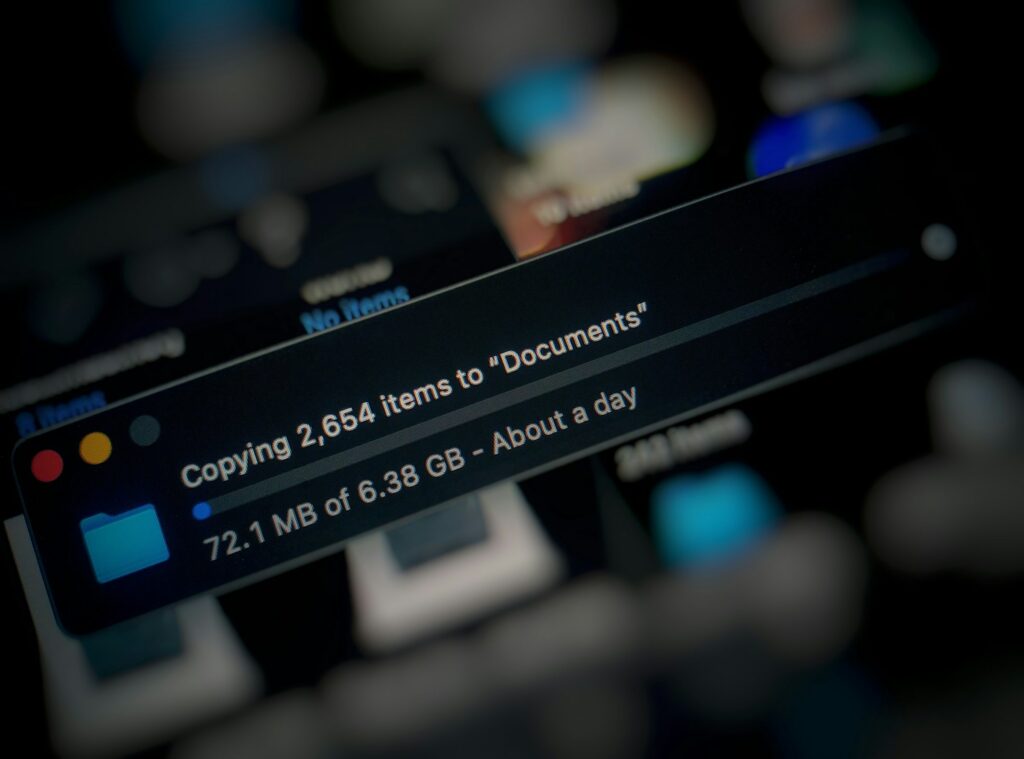
Google’s September 2025 update to Drive sharing permissions is a useful example of how these settings evolve over time. The update changed how restricted access behaves in shared folders and pushed administrators towards more consistent parent-folder controls, which underlines a wider point: sharing rules do not stand still, and what looked sensible a year ago may no longer behave quite the same way.
 The business risk is broader than a breach
The business risk is broader than a breach
When people hear “file sharing risk”, they often picture a catastrophic leak. That can happen, of course, but the more common problems are quieter:
- the wrong person gets access to commercially sensitive information
- old links stay open long after they should have expired
- client files end up spread across unmanaged platforms
- staff cannot tell which version is the real one
- nobody can reconstruct who shared what after an incident
That last point matters more than many teams realise. If a file containing pricing, payroll or personal data ends up in the wrong hands, the panic is usually worsened by poor evidence. If you cannot show who had access, who changed permissions and whether the file was downloaded, response becomes much harder.
For a broader look at how unmanaged tools create blind spots, our article on Taming Shadow IT in 2025 – A Practical SaaS Governance Plan is worth revisiting. File sharing chaos often starts as a shadow-IT problem before it becomes a security problem.
What “good” file sharing looks like
Secure file sharing does not mean locking everything down so tightly that staff resort to personal Gmail and USB sticks. It means creating a setup where sharing is:
- visible – you know where files are being shared
- controlled – access matches the work being done
- time-bound – external access expires unless there is a reason to keep it
- auditable – you can see who opened, downloaded or changed something
- consistent – staff know which tools they should use and why
A recent secure file-sharing market review from Kiteworks sums this up well: in practice, reliable secure collaboration now depends on zero-trust access, strong encryption, granular governance, immutable auditing and integrations that keep policy intact across different tools.
You do not need every enterprise bell and whistle to get the benefit. You do need to take the basics seriously.
Start with the simplest question: where are people sharing files?
Before changing permissions, start by mapping the real workflow. Ask:
- Which platforms do we officially use for file sharing?
- Which platforms do people actually use when they are in a hurry?
- Where do clients, contractors and suppliers receive documents from us?
- Which teams share files externally most often?
In many businesses the answer is “more places than we thought”. It may be Microsoft 365, Google Workspace, Dropbox, WeTransfer, client portals, project tools, and the occasional personal account that “just helped in a pinch”.
This is why a file-sharing clean-up usually sits halfway between a security exercise and an operations tidy-up. You are not only closing risk. You are reducing confusion.
The practical checklist that works
Here is a compact checklist that catches most of the real issues without turning into a week-long spreadsheet exercise.
1. Pick the approved tools
Decide which platforms are acceptable for company files. Keep the list short. If everything is approved, nothing is governed.
2. Review external sharing settings
Check whether users can create public links, invite guests freely, or share outside the organisation without approval. Tighten defaults where possible.
3. Remove stale guest access
Review guest users and external collaborators. If they are no longer attached to a live project, remove them.
4. Set expiry rules
Where the platform allows it, apply link expiry dates and guest-access reviews. Time limits are one of the easiest ways to reduce long-tail risk.
5. Restrict download rights on sensitive material
For especially sensitive files, consider view-only modes, watermarking, or download restrictions where the platform supports them.
6. Check ownership
Every shared site, folder or workspace should have a named owner. If nobody owns it, nobody will review it.
7. Audit “anyone with the link”
These links are convenient and often dangerous. Review them first, especially in finance, leadership and HR areas.
8. Tie the process to offboarding
When someone leaves, their shared links, external invites and delegated access should be reviewed as part of the same offboarding checklist, not later if someone remembers.
Why offboarding matters more than people think
One of the biggest sources of file-sharing risk is not an attacker. It is old access that nobody revoked.
A former contractor may still have a link to a working folder. A departed employee may have shared content with a personal email account to “work from home”. An agency may still be sitting in a client workspace long after the campaign wrapped up.
This is why file sharing and access governance belong together. They are really two views of the same question: who can still get to our information, and why?
Mustard’s piece on The End-of-Year Access Review: A Simple Checklist That Works fits neatly here. If your access review is sound, file-sharing clean-up becomes much easier because there are fewer stale permissions to chase.
 Build the controls around how people actually work
Build the controls around how people actually work
Security rules fail when they ignore reality. If your team shares large files with clients every day, the answer is not “never share files”. The answer is to give them a route that is easy, approved and monitored.
That means thinking practically:
- Can staff send clients a secure link without needing IT every time?
- Can project owners review external users quickly without raising tickets?
- Can finance share sensitive files in a way that does not depend on email attachments?
- Can leadership see a simple audit trail when something needs checking?
If the secure option is slower than the insecure one, people will route around it.
Policy matters, but defaults matter more
Most employees do not read file-sharing policy in detail. They follow what the system makes easy.
That is why the best improvements are often default settings rather than stern reminders. For example:
- guest access switched off unless specifically allowed
- expiry dates automatically added to external links
- notifications sent when a high-risk folder is shared externally
- regular prompts to re-confirm guest access
- only site owners able to create public links
CISA’s cloud-services security guidance makes the same broader point from a control perspective: secure collaboration depends heavily on strong default configurations, restricted administrative options and regular reviews of sharing behaviour.
Even if your organisation is nothing like a federal agency, the lesson still travels well. Good defaults prevent a large share of everyday mistakes.
What to measure
You do not need a security operations centre to know whether things are improving. A few steady metrics will tell you a lot:
- number of active guest users by platform
- number of public or unrestricted links still live
- percentage of shared spaces with a named owner
- number of stale external users removed this month
- number of file-sharing exceptions requested by staff
- percentage of sensitive sites reviewed this quarter
These measures are simple enough to discuss in a management meeting without the room glazing over. More importantly, they tell you whether the clean-up is becoming routine or quietly slipping.
A sensible 30-day tidy-up plan
Week 1: identify approved platforms, list the main external-sharing locations, and check who owns them.
Week 2: review guest access and remove old collaborators, starting with finance, leadership, HR and client-facing teams.
Week 3: tighten link settings, apply expiry rules where supported, and clean up “anyone with the link” shares.
Week 4: document the new rules, update offboarding steps, and report the before-and-after numbers so people can see progress.
This does not solve everything. It does give you a baseline that is far healthier than “we think it is probably fine”.
Keep the message simple
If you want staff to cooperate, avoid turning this into a sermon on governance. Tell them the plain truth:
We are not making sharing harder for fun. We are making it easier to trust.
That framing matters. People are far more willing to follow the rules when they can see that the goal is cleaner collaboration, fewer embarrassing mistakes and less time spent untangling old permissions.
Final thought
File-sharing problems rarely start with dramatic malice. They start with convenience, speed and good intentions. That is precisely why they are so persistent.
The answer is not to ban sharing or smother teams in red tape. It is to make the secure route the obvious route, clean up old access before it turns into a surprise, and keep enough visibility that you can answer simple questions when they matter.
If you want help untangling permissions, reviewing guest access and tightening your sharing setup without slowing the business down, contact Mustard IT.







 Build the controls around how people actually work
Build the controls around how people actually work




