As the race for digitally secure workplaces develops, business owners and IT departments are beginning to wonder if they have the necessary hardware to back up the complex software that guards the gates. The hardware necessary to power a secure internet is critical, but there are concerns that it’s playing catch up as the development of the internet and its associated risks gathers pace.
As cyber security protocols matures, there is a refocussing of priorities and resources. Previously it was enough for teams to control the flow of information through strategic use of firewalls and security. Now, in order to be both thorough and effective, cyber security must also investigate and teste the information that is allowed through the firewall. If traditional security practices screened the mail (data packets) for known malicious senders, consider that the new technology is also tasked with reading the mail before allowing it through the system. These extra layers of inspection draw down commensurate additional resources, but it’s expected to be completed in the same amount of time.
Providing the security infrastructure and computing power consumes far more resources than providing the relatively simple networks themselves. Security infrastructure is tasked with detecting malware and system intrusions. It is also expected to scan emails for potential phishing attempts, block malicious and fraudulent websites and enact multiple behaviour-control policies like scheduled product updates and password change requirements.
Security is also tasked with a lot more these days due to the larger ask from end to end devices. The perimeter is a lot more porous as methods of internet access are so diverse. Because there’s no longer a truly defined wall around a company’s resources, trying to shore up these external defences becomes difficult and intricate. Even then, it is naïve to rely on the wall as an impenetrable force – security must be present throughout the network, not just around it. These efforts require the knowledge and support of expert IT security consultants who can navigate the needs of your business and the growing cyber security threats.
These extraordinary tasks are requiring a far larger power source, which is why the quality of the hardware that supports your cyber security efforts will need to increase for it to perform at the required level.
More hardware doesn’t mean less software
It will remain critical to have excellent software in place to protect your business from cyber security threats. The innate flexibility of software makes it perfectly suited to adapting to the ever-shifting styles of cyber-attacks. It’s also true that the software will need to reflect different approaches to cyber security as scanning emails for malicious active content and protecting endpoint devices becomes non-negotiable.
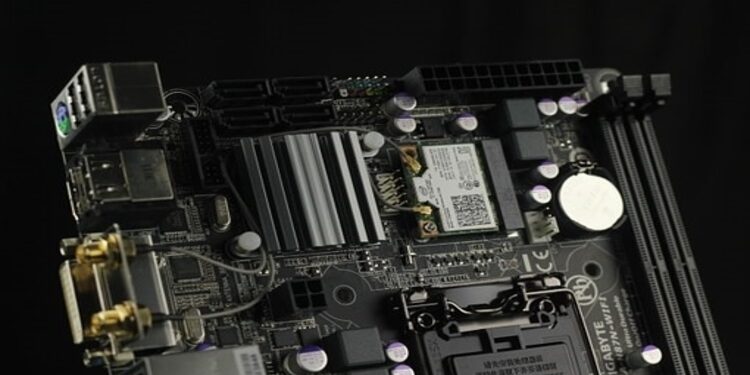
We’ve established that software is a critical tool in the fight against hackers and unauthorised intrusions. The software must be propelled by something powerful in order to elevate its true capabilities and have it operate and respond in a timely fashion. Specialised chips may be the answer. When these are optimised they can provide staggering leaps of computing power which helps to speed up processing times for security services. It doesn’t detract from cyber security software at all, rather it boosts overall performance.
Growing cost of security must be considered
Like anything, the value of an item or system must be realised before security can be established to protect it. The internet is like this, and so there has been a consistent game of catch-up being played out as developers push forward with new innovations. Security experts continue to develop new ways to protect sensitive data, and the costs to companies over time have increased significantly to reflect this. Upwards of 10% of tech budgets are now focussed on cyber security, up from a mere 2% around 20 years ago. There are predictions that this may increase near to the 50% mark over time. It’s clear that cyber security is a priority that UK businesses cannot afford to ignore. As the internet changes and develops (particularly with the possibility of application networking and the Internet 2.0) the computational demands and the ability to protect it from intrusion will only drive costs higher. The answer is to give it more power and the ability to protect itself from within. The IoT may serve as an example of this. Connected devices such as self-driving cars could have powerful hardware installed during the build phase that can help provide a secure communications network, and the cost of the hardware would be factored into the overall cost of manufacture.
Horizontal and vertical integration
How can IT departments make the best use of more powerful hardware in effort to boost data security? The key is using both horizontal and vertical integration strategies. This comprehensive approach should provide the most robust protection and the best performance. Integrating your networks horizontally requires a comprehensive security solution for all end points – mobile devices, desktop computers, laptop computers, email servers and the complete networks. As this becomes integrated, operations should become relatively automatic – smooth and uninterrupted. Very quickly, the demand for faster processing will become clear, so vertical integration of specialist hardware will be required to manage performance of the horizontal plane. End user experiences of this secure and high-performing digital environment should be simple, fast and secure.
How important is hardware for cyber security in the workplace? It really cannot be understated. The amount of cyber security software and applications available to IT teams and business owners is impressive. None of it will work to its full potential or capacity unless it has the computational hardware to back it up. Make the most of your investments by giving your software the strongest platform to succeed.
About Mustard IT, your cyber security partner
Mustard IT provide the design, build, installation and maintenance of secure business computer networks, including hardware selection and installation. Our trusted team are experienced able to explain complex issues to you in a language you’ll understand. Contact us today to find out how we can help you.