Security remains the number one priority for IT users and high profile breaches, such as those encountered by Facebook and Apple, continue to dent user confidence.
Increasingly, there is a feeling that the traditional user name and password may have had its day. We now have so many of these logins, they are getting harder to remember and, more importantly, hackers appear to be picking them off with relative ease.
So the search goes on for a more effective way to combat the threats and one method being adopted by a growing number of sites has become known as ‘two-factor authentication’.
Complexity through multiple identifiers
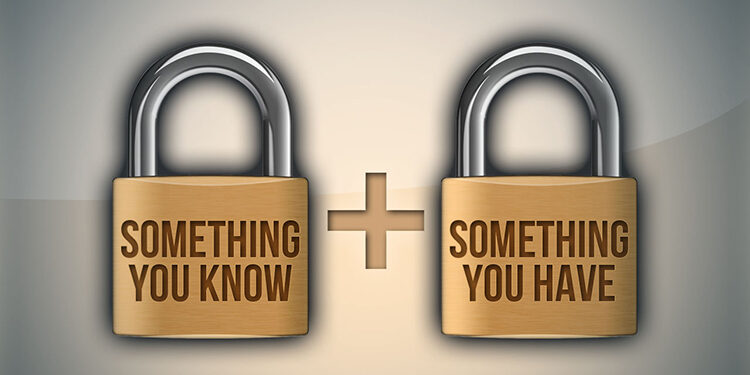
Rather than relying on a simple password of numbers, letters and punctuation marks, two-factor authentication (2FA) is a system which enables a program or website to confirm your identity using two out of three possible identifiers.
There are three types of identifier: something you know, something you have and something you are. An easy example to help illustrate 2FA is a bank card. In order to withdraw cash, you require something physical – the card – but also, something you know – the PIN number.
Something you know
A standard password is something you know but pets’ names and favourite football teams are slowly giving way to more innovative methods such as the pattern-based keys commonly seen on Android devices. Either way, ‘something you know’ is generally based on information users provide themselves when setting up an account.
Something you have
This refers to an object in the user’s possession and a simple example would be a door key, which is a device designed to allow a barrier to be unlocked. The same principle applies with 2FA, although smartphone apps and other dedicated devices, such as the pin number generators being distributed by banks these days, are acting as the modern equivalent to house keys. A good illustration of this principle is the way that Google has started using SMS to send a randomly generated code to the user. This code then has to be entered after the initial password as the second identifier – something you know and something you have.
Something you are
The first two categories above are still the most popular but technological advances mean that users are also able to identify themselves using their bodies. Fingerprint scanning is available on iPhones and other devices whilst facial recognition and even retina scanning is following closely behind. This technology may be expensive but it can be very accurate so we can expect to see vendors using it more in the future to reassure their customers.